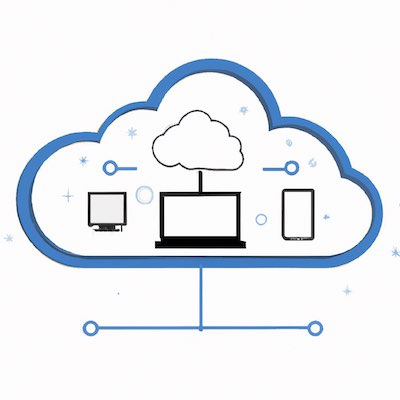
Today, cloud computing is revolutionizing the way businesses operate, allowing them to store and access data on a remote server and access it from any device. But, like any technology, there are risks associated with cloud computing. In this blog post, we're going to explore the risks associated with cloud computing and provide a guide to help you navigate them successfully.
Today, cloud computing is revolutionizing the way businesses operate, allowing them to store and access data on a remote server and access it from any device. But, like any technology, there are risks associated with cloud computing. In this blog post, we're going to explore the risks associated with cloud computing and provide a guide to help you navigate them successfully.
Introduction to Cloud Computing and Associated Risks
Cloud computing is a powerful tool that allows businesses to store and access their data remotely from any device, in any location. But, like any technology, there are risks associated with cloud computing. These risks could include data loss, data breaches, and security vulnerabilities. It's important to be aware of these risks and know how to manage them.
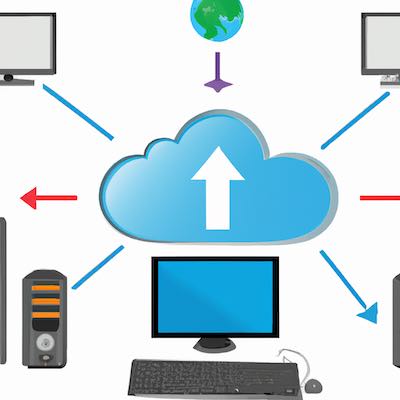
The first step in understanding the risks associated with cloud computing is to understand the basics of cloud computing. Cloud computing is a type of technology that allows businesses to store and access their data on a remote server, rather than on a local server or computer. This allows businesses to access their data from any device, in any location.
The benefits of cloud computing are numerous: it can reduce costs, increase storage capacity, and enable businesses to access their data from any device. However, it also comes with risks, such as data loss, data breaches, and security vulnerabilities. It's important to be aware of these risks and know how to manage them.
Types of Cloud Computing Risks
When it comes to cloud computing, there are a number of risks that businesses must be aware of. These can be divided into three main categories: data loss, data breaches, and security vulnerabilities.
Data loss is a risk that can occur if a cloud computing system fails or is otherwise compromised. This can lead to the loss of important data, which can have a significant impact on a business.
Data breaches are a risk that can occur if a malicious actor gains access to a cloud computing system. This can lead to the theft of sensitive data, which can have a significant impact on a business.
Security vulnerabilities are a risk that can occur if a cloud computing system is not properly configured or maintained. This can lead to the exploitation of vulnerabilities, which can have a significant impact on a business.
It's important to be aware of these risks and know how to manage them.
Assessing Cloud Computing Risks
The first step in managing cloud computing risks is to assess them. This involves taking an in-depth look at the cloud computing system and its associated risks. This includes performing a thorough security audit, examining the system architecture, and testing the system for vulnerabilities.
When assessing cloud computing risks, it's important to look at the system as a whole. This means looking at the system architecture, the system infrastructure, and the system security. By understanding the system as a whole, it's possible to identify gaps and weaknesses that could be exploited.
It's also important to consider the data that is being stored on the cloud. This includes looking at the type of data being stored, who has access to it, and how it is being secured. By understanding the data, it's possible to identify potential risks and take steps to mitigate them.
Strategies for Managing Cloud Computing Risks
Once the risks associated with cloud computing have been identified, it's important to take steps to manage them. This involves implementing a risk management strategy that includes policies and procedures to reduce the likelihood of a data breach or security vulnerability.
The first step in managing cloud computing risks is to implement a robust security system. This includes installing firewalls, encryption software, and other security measures to protect the system from malicious actors. It's also important to monitor the system for any signs of an attack or breach.
It's also important to implement strong access control measures. This includes setting up user accounts, assigning permissions, and setting up authentication protocols to ensure only authorized users can access the system.
It's also important to create policies and procedures for managing data. This includes setting up procedures for handling sensitive data, backing up data, and ensuring that the data is secure.
Finally, it's important to regularly monitor the system for any signs of an attack or breach. This includes scanning for malicious activity, monitoring for suspicious behavior, and responding quickly to any threats.
Cloud Security Best Practices
When it comes to cloud security, there are several best practices that businesses should follow. These include:
- Implementing a robust security system.
- Setting up user accounts and assigning permissions.
- Setting up authentication protocols.
- Creating policies and procedures for handling sensitive data.
- Backing up data regularly.
- Scanning for malicious activity.
- Monitoring for suspicious behavior.
- Responding quickly to any threats.
By following these best practices, businesses can ensure that their cloud computing systems are secure and their data is protected.
The Role of Governance in Risk Management
The role of governance in risk management is to ensure that the organization is taking steps to mitigate risks, such as data loss or data breaches. This involves setting up policies and procedures for managing risks, as well as monitoring the system for any signs of an attack or breach.
When it comes to governance, it's important to have a clear chain of command. This means that there should be a clearly defined leader or team responsible for managing risk. This team should have the authority to make decisions and implement policies and procedures.
It's also important to have a system for monitoring the system for any signs of an attack or breach. This includes scanning for malicious activity, monitoring for suspicious behavior, and responding quickly to any threats.
Using Third-Party Cloud Services
When it comes to cloud computing, businesses may choose to use third-party cloud services, such as Amazon Web Services or Microsoft Azure. These services can provide businesses with access to powerful cloud computing resources, such as storage and computing power.
When using third-party cloud services, it's important to understand the risks associated with the service. This includes understanding the security measures that are in place, the type of data that is being stored, and the access controls that are in place.
It's also important to ensure that the third-party service is compliant with any applicable regulations. This includes ensuring that the service is compliant with data privacy laws or industry regulations.
Finally, it's important to ensure that the third-party service is secure. This includes ensuring that the service is regularly monitored for any signs of an attack or breach.
Automation and Monitoring for Cloud Security
When it comes to cloud security, automation and monitoring are key. Automation can help to reduce the risk of data loss or data breaches, while monitoring can help to detect any suspicious activity.
Automation can be used to help manage cloud security. This includes automating the process of setting up user accounts and assigning permissions, as well as automating the process of setting up authentication protocols. Automation can also be used to help manage the system for any signs of an attack or breach.
Monitoring is also an important part of managing cloud security. This includes monitoring the system for any suspicious activity, as well as monitoring for any changes in the system infrastructure or security measures.
Conclusion
In conclusion, cloud computing is an incredibly powerful tool that can provide businesses with access to powerful computing resources. However, it also comes with risks, such as data loss, data breaches, and security vulnerabilities. It's important to be aware of these risks and know how to manage them.
This blog post has provided a guide to help you navigate the risks associated with cloud computing. We have discussed the types of risks associated with cloud computing, how to assess them, strategies for managing them, and cloud security best practices. We have also discussed the role of governance in risk management and the importance of using third-party cloud services. Finally, we have discussed the importance of automation and monitoring for cloud security.
By following these guidelines, businesses can ensure that their cloud computing systems are secure and their data is protected.